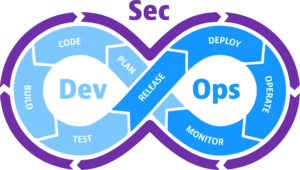
Over a decade ago, Shannon Lietz coined the term DevSecOps with the vision of integrating security seamlessly into the IT development and operations landscape. The primary aim was to secure a dedicated seat for security at the table where IT developers and operators strategize. A decade later, it’s imperative to evaluate how far security has journeyed within the DevSecOps realm—whether the culture, practices, and tooling have matured sufficiently to facilitate the swift, reliable, and secure release of technology into production.
The recently published SANS DevSecOps Survey serves as a beacon, shedding light on the significant traction gained by organizations in embracing security practices within their development workflows. Over 50% of respondents claimed to resolve critical security risks and vulnerabilities within an impressive seven days or less. However, the survey also reveals a paradox—while almost 30% of organizations deploy to production weekly, merely 20% assess or test for security vulnerabilities at a similar velocity. This disjunction raises questions about the alignment of development and security practices.
In the journey toward mature security and continuous deployment, the adoption rates for DevSecOps practices highlight both progress and areas of improvement. Automation boasts a commendable 61% adoption rate, reflecting the industry’s commitment to streamlining processes. However, continuous integration (CI) lags slightly behind at 50%, indicating that many organizations are still navigating the path toward fully integrated development and security workflows.
TABLE OF CONTENTS
1. The Landscape of DevSecOps Practices
- Shifting Left: The Evolution of Security in Development
- The Paradox of Deployment Velocity vs. Security Assessment
2. The Heart of DevSecOps: Top 3 Security Best Practices
- Institute Security in API-First Strategies
- APIs: The Cornerstone of Modern DevOps
- API Security Trends: Insights from Wallarm’s API ThreatStats Report
- Automate Code Scanning
- From Manual Processes to Automated Vigilance
- The Critical Role of Early Threat Detection
- Standardize Data Observability Practices
- From Application Logging to Modern Observability Tools
- Extending Observability to Security, DataOps, and MLops
3. The Nuances of Security Practices in DevSecOps
- Navigating Over 25 Security Practices from the SANS Survey
- Code-Based Methods: Adoption, Challenges, and Impact
4. Expert Voices: Fundamentals of DevSecOps
- Insights from Industry Leaders: Building Security into DevOps
- Balancing Security Guardrails and Development Velocity
5. Prioritizing Security Measures: Business Goals, Risks, and Compliance
- Determining Which Security Practices to Prioritize
- Aligning Security with Business Goals, Risks, and Compliance
6. Beyond the Top 3: A Comprehensive Security Landscape
- Third-Party Penetration Testing
- Security Training and Awareness
- Web Application Firewall (WAF) Implementation
- Container Security Scanning and Cloud-Native Application Protection Platforms
7. Continuous DevSecOps: The Call for Standardization
- Addressing Risks Through Ongoing Security Practices
- Building a Foundation for Continuous DevSecOps Excellence
In conclusion, the journey of DevSecOps over the past decade reveals progress, challenges, and a call for continuous improvement. As organizations strive for a more secure and integrated future, the essay delves into key practices, expert insights, and the broader landscape of security within DevSecOps.


