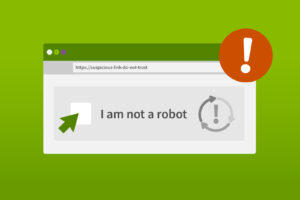
A new web-based attack is targeting Windows users with fake CAPTCHA pages designed to install malware through simple keyboard commands. According to reporting highlighted by Windows Central, hackers are using deceptive verification prompts to trick people into running malicious code on their own systems.
The attack begins with a counterfeit CAPTCHA screen that looks like a routine “prove you’re human” check. Instead of clicking images or solving puzzles, users are instructed to press Windows key + R to open the Run dialog, then press Ctrl + V and hit Enter. These steps execute a command that the page secretly copied to the clipboard in the background.
That command launches PowerShell and downloads a piece of malware known as StealC without obvious warning. The information-stealing tool can harvest sensitive data including browser logins, Outlook credentials, Steam accounts, and even cryptocurrency wallet details, according to security researchers at Level Blue.
The tactic relies on social engineering rather than a traditional Windows software flaw. By mimicking legitimate security checks, attackers persuade users to run commands themselves. However, legitimate websites never ask visitors to open system tools like the Windows Run prompt or paste commands as part of a CAPTCHA process.
Experts recommend ignoring any site that asks you to execute keyboard shortcuts or system commands during verification steps. Keeping antivirus software active, updating Windows regularly, and avoiding suspicious websites can also reduce the risk of infection. Clearing the clipboard and running a malware scan is advised if you believe you may have followed such instructions.
The campaign highlights a growing trend: attackers are increasingly exploiting user trust and familiar interfaces rather than relying solely on technical vulnerabilities to spread malware.